Threat Assessment Pp Pdf Vulnerability Computing Databases

Threat Assessment Pp Pdf Vulnerability Computing Databases Threat assessment pp free download as powerpoint presentation (.ppt .pptx), pdf file (.pdf), text file (.txt) or view presentation slides online. vulnerability assessments are used to discover weaknesses in database systems. there are two main assessment methods: quantitative and qualitative. The aim of this study is to explore possible database security threats in a tps, along with some security challenges, and mitigation techniques to these threats.

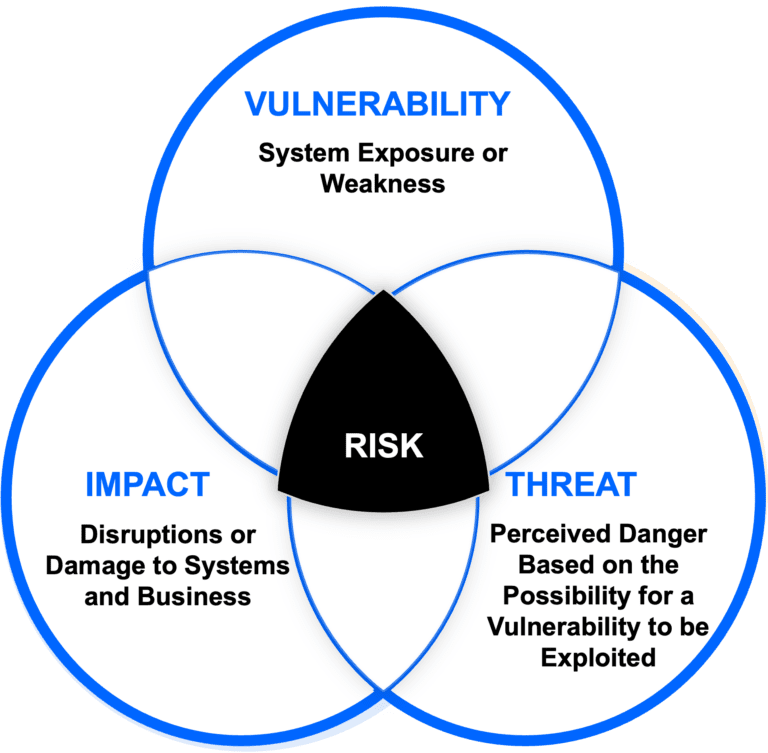
How To Write A Vulnerability Assessment Report Pdf Vulnerability Based on the results, this paper points out some issues related to vulnerability databases handling that impact the effectiveness of certain vulnerability identification methods. The primary objective of this risk assessment framework is to provide a robust and comprehensive approach for addressing all types of threats, vulnerabilities, and countermeasures in database systems. Risk assessments are a key part of effective risk management and facilitate decision making at all three tiers in the risk management hierarchy including the organization level, mission business process level, and information system level. Keeping these databases up to date is crucial for effective vulnerability scanning, as they form the basis on which scanning tools assess and identify vulnerabilities.

A Comprehensive Guide To Vulnerability Analysis Identifying Risk assessments are a key part of effective risk management and facilitate decision making at all three tiers in the risk management hierarchy including the organization level, mission business process level, and information system level. Keeping these databases up to date is crucial for effective vulnerability scanning, as they form the basis on which scanning tools assess and identify vulnerabilities. This approach provides actionable information on inherent vulnerabilities and database configuration elements that may make your databases vulnerable to attack, lead to regulatory compliance issues, or make them fail to comply with your information security policy. Provides several features for probing computer networks, including host discovery and service and operating system detection; extensible feature set with many scripts that provide more advanced services detection, vulnerability detection and other features. These playbooks provide fceb agencies with a standard set of procedures to identify, coordinate, remediate, recover, and track successful mitigations from incidents and vulnerabilities affecting fceb systems, data, and networks. With the rapid adoption of cloud computing across industries, securing databases in cloud environments has become a critical concern. this paper presents a comprehensive review of database.
Vulnerability Assessment Satius Security This approach provides actionable information on inherent vulnerabilities and database configuration elements that may make your databases vulnerable to attack, lead to regulatory compliance issues, or make them fail to comply with your information security policy. Provides several features for probing computer networks, including host discovery and service and operating system detection; extensible feature set with many scripts that provide more advanced services detection, vulnerability detection and other features. These playbooks provide fceb agencies with a standard set of procedures to identify, coordinate, remediate, recover, and track successful mitigations from incidents and vulnerabilities affecting fceb systems, data, and networks. With the rapid adoption of cloud computing across industries, securing databases in cloud environments has become a critical concern. this paper presents a comprehensive review of database.
Comments are closed.