Attacker Crypter V0 9 Unveiling A Powerful Tool For Evading
Attacker Crypter V0 9 Unveiling A Powerful Tool For Evading Attackcrypt, an open source “crypter,” was recently used by cybercriminals to hide malware binaries and avoid antivirus detection. a crypter is a kind of software that can encrypt, obfuscate, and alter malicious code to make detection by security tools more difficult. They work similar to packers, by taking a malware binary and applying a series of modifications, obfuscations and encryptions to output a binary that evades one or more avs. the goal is to remain fully undetected, or fud in the hacking jargon, while maintaining its (often malicious) functionality.
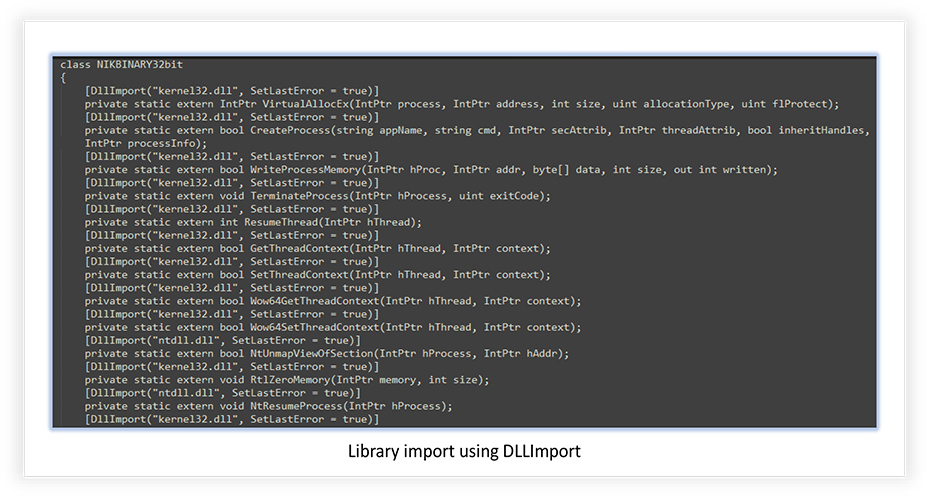
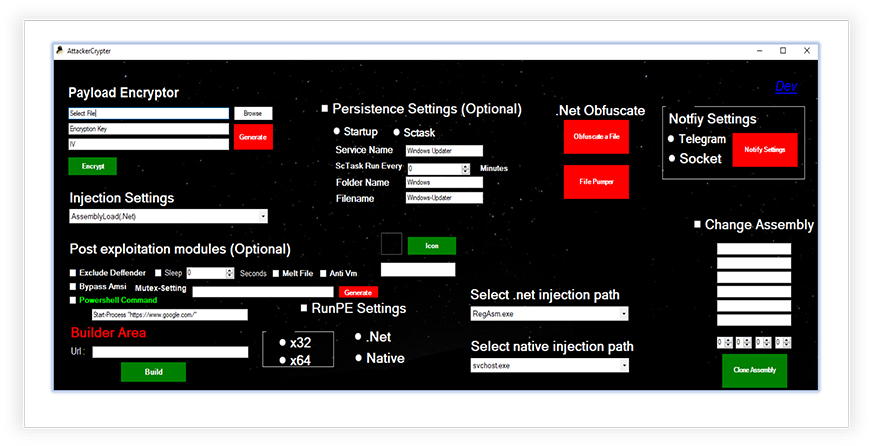
Attacker Crypter V0 9 Unveiling A Powerful Tool For Evading For malicious actors, open source crypters offer a readily available solution for evading detection by antivirus software and for successfully delivering their malicious payloads. these tools can be easily customised and adapted to suit the needs of specific malware campaigns. Crypters are tools, techniques, or methods that adversaries leverage to encrypt, obfuscate, or otherwise modify malicious code to evade detection technologies. loaders are a type of malware intended specifically to deliver additional payloads, like stealers, cryptominers, or ransomware. Attacker crypter; a potent malware tool – cyfirma research team discovers the emergence of attacker crypter; a powerful and easy to use software designed to encrypt, obfuscate, and manipulate malicious code, rendering it harder to detect by security tools and antivirus software. One noteworthy tool that has emerged is attacker crypter. a crypter is a type of software that can encrypt, obfuscate and manipulate malicious code to make detection harder by the security tools, and is used by cybercriminals to create malware that can deceive security checks and av detections.
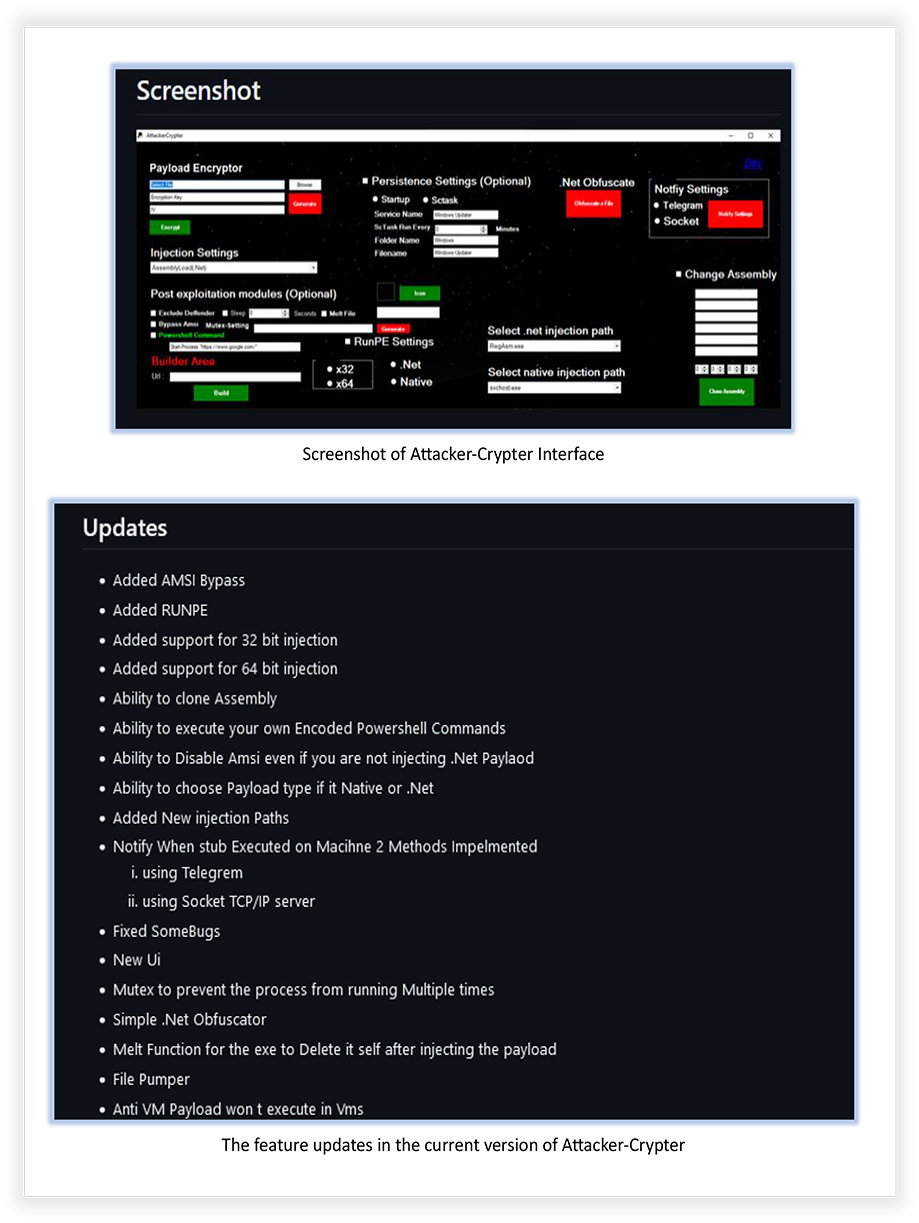
Attacker Crypter V0 9 Unveiling A Powerful Tool For Evading Attacker crypter; a potent malware tool – cyfirma research team discovers the emergence of attacker crypter; a powerful and easy to use software designed to encrypt, obfuscate, and manipulate malicious code, rendering it harder to detect by security tools and antivirus software. One noteworthy tool that has emerged is attacker crypter. a crypter is a type of software that can encrypt, obfuscate and manipulate malicious code to make detection harder by the security tools, and is used by cybercriminals to create malware that can deceive security checks and av detections. One noteworthy tool that has emerged is attacker crypter. a crypter is a type of software that can encrypt, obfuscate and manipulate malicious code to make detection harder by the security tools, and is used by cybercriminals to create malware that can deceive security checks and av detections. Instead of protecting the payload the tool converts it into encrypted data that is stored as a string. this string must then be uploaded to a "drop site" but the operator and then the "drop site" url placed in the tool to generate the "stub". #cyfirma researchers have unearthed a tool called attacker crypter, which is not only powerful and easy to use, but also enables cybercriminals to encrypt, obfuscate, and manipulate. Virustotal cooperates with many antiviruses and shares its up to date database. in order for this crypter to work for a longer time, you must follow this simple rule.
Attacker Crypter V0 9 Unveiling A Powerful Tool For Evading One noteworthy tool that has emerged is attacker crypter. a crypter is a type of software that can encrypt, obfuscate and manipulate malicious code to make detection harder by the security tools, and is used by cybercriminals to create malware that can deceive security checks and av detections. Instead of protecting the payload the tool converts it into encrypted data that is stored as a string. this string must then be uploaded to a "drop site" but the operator and then the "drop site" url placed in the tool to generate the "stub". #cyfirma researchers have unearthed a tool called attacker crypter, which is not only powerful and easy to use, but also enables cybercriminals to encrypt, obfuscate, and manipulate. Virustotal cooperates with many antiviruses and shares its up to date database. in order for this crypter to work for a longer time, you must follow this simple rule.
Attacker Crypter V0 9 Unveiling A Powerful Tool For Evading #cyfirma researchers have unearthed a tool called attacker crypter, which is not only powerful and easy to use, but also enables cybercriminals to encrypt, obfuscate, and manipulate. Virustotal cooperates with many antiviruses and shares its up to date database. in order for this crypter to work for a longer time, you must follow this simple rule.
Attacker Crypter V0 9 Unveiling A Powerful Tool For Evading
Comments are closed.