A Developer Guide To Performing A Tls Handshake Pinkhat Code

Tls Handshake Pdf Transport Layer Security Public Key Cryptography Learn the step by step process of performing a tls handshake and get tls 1.3 handshake explained for better development. I've helped numerous companies improve traffic to their sites including microsoft, pure storage, adobe, rackspace, cloudlinux, solarwinds, ibm and several more. i've had content featured in techcrunch and fastcompany. i've also ghostwritten technical books for o'reilly. contact me to see what i can do for you at jennifer@pinkhatcode .
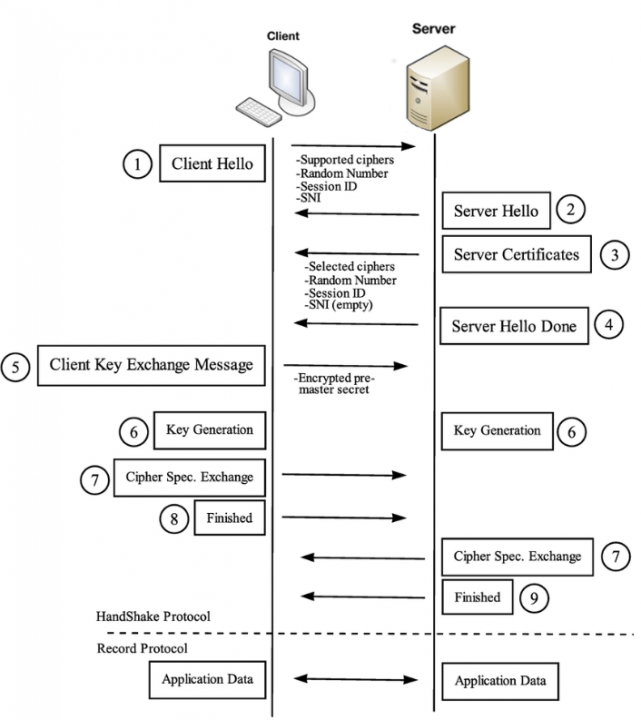
A Developer Guide To Performing A Tls Handshake Pinkhat Code You probably know that your http requests will likely use tls (transport layer security) to create an encrypted connection, but most developers don’t know what happens in a client server connection when it’s encrypted using tls. You probably know that your http requests will likely use tls (transport layer security) to create an encrypted connection, but most developers don’t know what happens in a client server connection when it’s encrypted using tls. The transport layer security (tls) handshake is a critical component of modern internet communication, enabling secure data transfer between two parties. in this article, we'll delve into the intricacies of the tls handshake protocol, exploring each step and the cryptographic algorithms involved. This project, conducted as part of ece 628 – computer security at the university of waterloo, implements rsa & ephemeral dhe handshakes between client & server from scratch for tls ssl protocol (tls 1.2).

A Developer Guide To Performing A Tls Handshake Pinkhat Code The transport layer security (tls) handshake is a critical component of modern internet communication, enabling secure data transfer between two parties. in this article, we'll delve into the intricacies of the tls handshake protocol, exploring each step and the cryptographic algorithms involved. This project, conducted as part of ece 628 – computer security at the university of waterloo, implements rsa & ephemeral dhe handshakes between client & server from scratch for tls ssl protocol (tls 1.2). The tls handshake is essentially a negotiation protocol that establishes a secure channel between client and server. think of it as two parties agreeing on a secret language before they start their actual conversation. Master the tls handshake to optimize your app's https performance and security. learn the step by step process, common challenges, and best practices for building robust and secure applications. This document provides a detailed explanation of the transport layer security (tls) handshake process, which forms the foundation of secure https communication. The tls handshake is one of the unsung heroes of the modern web. it happens in the blink of an eye, but it lays the foundation for secure, trustworthy communication online.

The Tls Handshake Protocol Messages Sequence By Wentz Wu Issap Issep The tls handshake is essentially a negotiation protocol that establishes a secure channel between client and server. think of it as two parties agreeing on a secret language before they start their actual conversation. Master the tls handshake to optimize your app's https performance and security. learn the step by step process, common challenges, and best practices for building robust and secure applications. This document provides a detailed explanation of the transport layer security (tls) handshake process, which forms the foundation of secure https communication. The tls handshake is one of the unsung heroes of the modern web. it happens in the blink of an eye, but it lays the foundation for secure, trustworthy communication online.

What Is A Tls Ssl Handshake And How It Works This document provides a detailed explanation of the transport layer security (tls) handshake process, which forms the foundation of secure https communication. The tls handshake is one of the unsung heroes of the modern web. it happens in the blink of an eye, but it lays the foundation for secure, trustworthy communication online.
Comments are closed.