58 Ssl Handshake Pdf Transport Layer Security Public Key Certificate

58 Ssl Handshake Pdf Transport Layer Security Public Key Certificate 58 ssl handshake free download as pdf file (.pdf), text file (.txt) or read online for free. the document discusses ssl and tls protocols, which provide security between web servers and browsers. • uses the secret keys established in the handshake protocol to protect confidentiality, integrity, and authenticity of data exchange between the client and the server.

Tls Handshake Pdf Transport Layer Security Public Key Cryptography After server’s certificate is verified, client generates random number, called pre master secret. client encrypts pre master secret using server’s public key and sends to the server. length of the key depends on the public key algorithm used. The document describes a 4 phase ssl handshake process with two way authentication using certificates. in phase 1, the client and server exchange random numbers and agree on encryption settings. The document provides an overview of tls ssl handshake, explaining its importance in web security through encryption and authentication. it details the steps involved in the handshake process, including client and server messages, key exchanges, and the types of ssl certificates available. In this chapter, we first discuss how transport layer security works. we specifically focus on the two most important aspects of tls: handshake and data transmission.
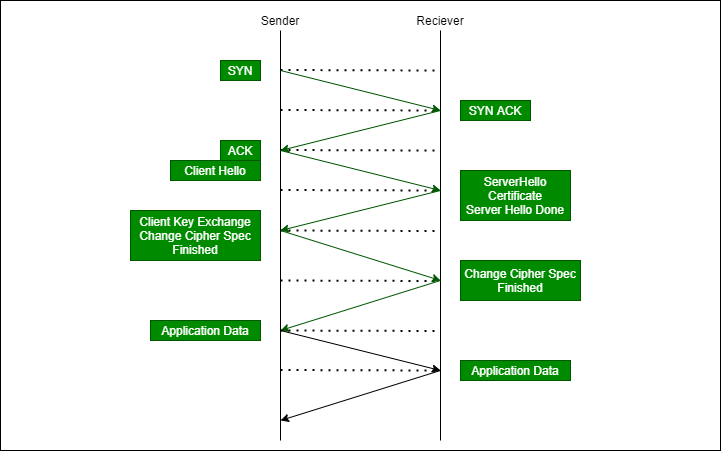
Transport Layer Security Tls Handshake Geeksforgeeks The document provides an overview of tls ssl handshake, explaining its importance in web security through encryption and authentication. it details the steps involved in the handshake process, including client and server messages, key exchanges, and the types of ssl certificates available. In this chapter, we first discuss how transport layer security works. we specifically focus on the two most important aspects of tls: handshake and data transmission. Understanding tls and the handshake free download as pdf file (.pdf), text file (.txt) or view presentation slides online. This abstract examines various security challenges in cloud environments and explores how distributed systems can provide solutions to enhance security posture. This can contain private key and certificate chain material. its used preferentially by windows systems, and can be freely converted to pem format through use of openssl. Solution: bob sends different random nonce for each connection. this causes encryption keys to be different for each connection.
Comments are closed.